# Volatility2 Basics (Linux)

### 1. Introduction
A memory dump is provided in the home directory of the root user. You have to use [Volatility](https://github.com/volatilityfoundation/volatility) to answer the following questions:
1. Which command is used to list all profiles supported by Volatility?
2. What is the name of the profile which is present for Ubuntu Linux?
3. Which command can be used to extract the CPU details from the memory dump?
4. Which command can be used to retrieve the list running processes from memory dump?
5. Which command can be used to show the processes in the parent-child relationship format?
6. Which command can be used to extract the list of open TCP connections from the memory dump?
7. What was the IP address of the machine on which the memory dump was taken?
8. Which command can identify the applications (which are using a promiscuous socket) from the memory dump?
9. Which command can be used to recover the bash command history from the memory dump?
### 2. Answers
To list all profiles I can use the command:
`vol.py --info`
The profile name for linux ubuntu is:
`LinuxUbuntu-16_04-4_15_0_45-genericx64`

To identify the cpu I'll use the following command:
`vol.py -f memory_dump.img linux_cpuinfo`
`vol.py -f memory_dump.img linux_pslist`

The get a list of processes I use the following command:
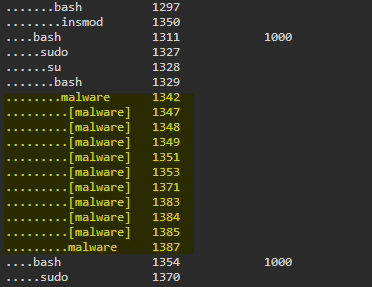
`vol.py -f memory_dump.img linux_pstree`
To get a list of open tcp connections I use the following command:
`vol.py -f memory_dump.img linux_netstat`
To reveal the ip adress from memory I'll use the following command:
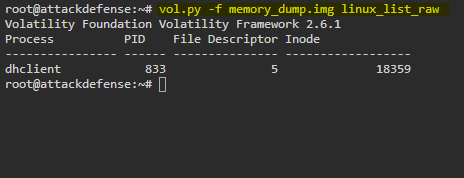
Identify applications which are using promiscious connections:
Reveal bash command history:
`vol.py -f memory_dump.img linux_bash`

### 3. Summary
{% embed url="" %}