# Tshark Exercise
### 1. Introduction
> You are a security investigator at a relatively small company. You have just been notified that there might have been a computer virus going around the office and infecting the workstations. Your team managed to capture the network traffic in the office for you to analyze. The `.pcap` file (a data file created using Wireshark that contains the packet data of a network) has been transferred to your remote Ubuntu workstation. In this module, you will use TShark, a free alternative tool to capture network traffic and view already captured data.
In some cases you might not have access to a graphical user interface and therefore can't use tools like **Wireshark**. This module is focused on basic `.pcap` file analysis using TShark. During the module, you will be using TShark to capture files and other data from the `.pcap` file.
### 2. PCAP Analysis
Without an input file, TShark simply acts like tcpdump. It will capture traffic from the first available network and display its packets to standard output. Alternatively, you can use the `-r` flag to specify the network capture file
```
tshark -r network_capture.pcap
```
This may seem complicated, but remember that the command-line output of TShark mirrors the Wireshark interface! The fields from left to right in the command line output are:
| Packet number | Time | Source | Destination | Protocol | Length | Info |
|---|
| 35 | 29.947879 | 192.168.0.55 | 192.168.0.91 | HTTP | 423 | HTTP/1.1 200 OK |
The **Time** field shows when the packet was captured. The **Source** and **Destination** fields show the source IP and destination IP of that packet. The **Protocol** field displays the protocol used. The **Length** field shows the length of the packet. And finally, the **Info** field displays any additional info about the packet.
You can filter these packet summaries by piping TShark's output into **grep**. For example, this command will output the packets with a “200 OK” HTTP status code.
```
tshark -r network.pcap | grep "200 OK"
```

### 3. Reveal IP address and find suspiscious file
Investigate the `.pcap` file with **TShark:**
The `.pcap` file location is `/home/student/capture3.pcap`.
* The suspicious file you need to investigate is named `upgrade-windows-defender.exe`.
* You are currently interested in **HTTP traffic**
How many times has the malicious file been downloaded in the network?
Name one of the IP addresses where the malicious file was downloaded from.
First we have to set a filter:
```
http.request.method == GET # Filter out all GET http requests
```
With just that filter alone, we can't see anything interessting so far, because there are to many http get requests in that capture:

Beside the http get request filter we can grep the name of the suspiscious file:
```
tshark -r /home/student/capture3.pcap "http.request.method==GET" | grep "upgrade-windows-defender.exe"
```

As we can see the suspiscious file was downloaded 10 times and one of the IP's where the file was downloaded from is: **113.10.152.202**
### **4. Extract the file from pcap**
In a [previous exercise](https://cas-cyber.gitbook.io/cas-cybersecurity/malware-analysis/yara/tcp-dump-analysis) I did allready learn different methods howto extract files from a tcp dump file. In this case I'll use tshark to extract files relating to http. It's not possible to extract just a single file. I've to extract everything:
```
tshark -r network.pcap --export-objects http,/home/student
```
I'll grep for upgrade-windows-defender and I'll also take the md5 hashes.

Just a short analysis from virustotal shows that the file is maliscious!

### 5. Find passwords
You can also specify the output format for the decoded packet data using the `-T` flag. For example, this command will display all **HTTP GET requests** in JSON format.
```
tshark -r network.pcap -T json "http.request.method==GET"
```
Finally, you can process the output from TShark by piping it into other command-line tools such as grep.
Since your preliminary investigation on the virus is done, you decide to analyze the rest of the `.pcap` file to see if everything is secure and the traffic encrypted. If malware has been moving around in the network you should make sure that there are no plain text passwords moving around as well.
You remember that you can easily filter what you are looking for in the `.pcap` file. When dealing with passwords, you need to filter for **POST requests**.
Investigate the `.pcap` file further with TShark and answer the questions:
1. What is the password used by the user **MozellRobel-EiZ**?
2. What is the password for the user **Manager**?
3. What is **Archie Shepherd's** username?
To get the password of the user **MozellRobel-EiZ**, run:
```
tshark -r capture3.pcap -T json "http.request.method == POST && http.file_data contains MozellRobel-EiZ" | grep password
```

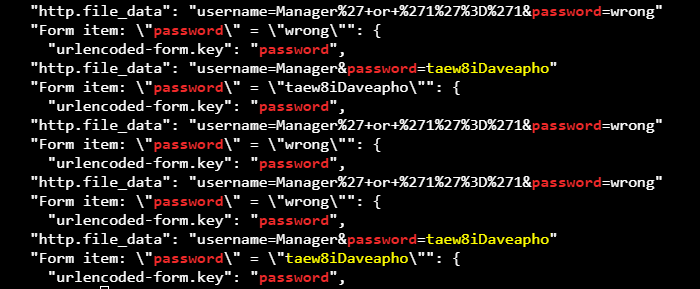
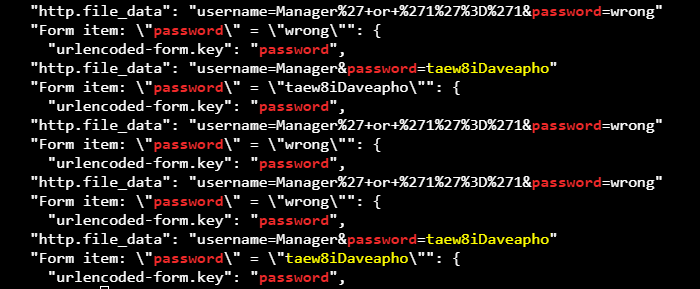
To get the password of the user **Manager**, run:
```
tshark -r capture3.pcap -T json "http.request.method == POST && http.file_data contains Manager" | grep password
```
To get the username of **Archie Shepherd**, run:
```
tshark -r capture3.pcap -T json "http.request.method == POST && http.file_data contains Shepherd" | grep username
```