# Reconnaissance
### Passive/Active Information Gathering
#### Active Reconnaissance
In this process, you will directly interact with the computer system to gain information. This information can be relevant and accurate. But there is a risk of getting detected if you are planning active reconnaissance without permission. If you are detected, then system admin can take severe action against you and trail your subsequent activities.
#### Passive Reconnaissance
In this process, you will not be directly connected to a computer system. This process is used to gather essential information without ever interacting with the target systems
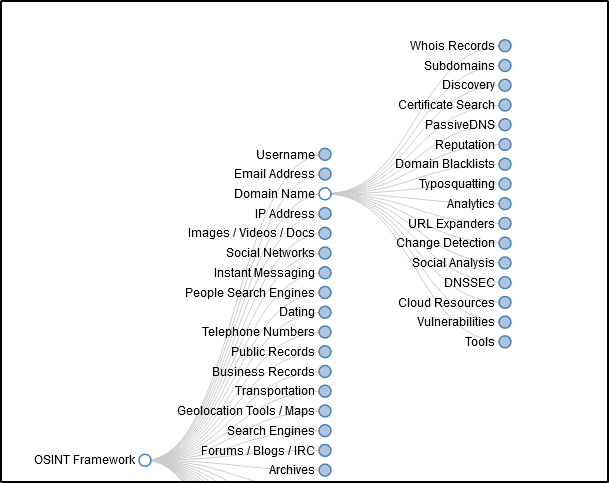
A good start for this is the OSINT Framework, which provides a powerfull wiki: [https://www.osintframework.com ](https://www.osintframework.com/)