# Velociraptor P1
### 1. Introduction
Velociraptor is an advanced digital forensic and incident response tool that enhances your visibility into your endpoints. In this exercise we'll setup a velociraptor server based on linux and connect a windows client to it. Further we'll collect our first artefact.
### 2. Setup
Prerequisite:
* Linux VM ()
* Windows 10 VM ()
Velociraptor can be run on windows, linux and macOSX. In this case I'll run velociraptor on a virtual linux machine and I'll setup a windows box which is connected to the velociraptor server.
[Original Lab](https://samsclass.info/152/proj/IR371.htm) developed by SAM BOWNE:
{% embed url="" %}
### 3. Installation
```
mkdir Velociraptor
cd Velociraptor
wget https://github.com/Velocidex/velociraptor/releases/download/v0.6.4-2/velociraptor-v0.6.4-2-linux-amd64
chmod +x velociraptor-v0.6.4-2-linux-amd64
./velociraptor-v0.6.4-2-linux-amd64 config generate > velociraptor.config.yaml
```
Edit the `velociraptor.config.yaml` configuration file and replace every localhost or 127.0.0.1 entry with the ip address of the virtual machine.

`mv velociraptor.config.yaml /etc`
Set administrator password:
```
./velociraptor-v0.6.4-2-linux-amd64 --config /etc/velociraptor.config.yaml user add admin --role administrator
```
Start Velociraptor GUI:
```
./velociraptor-v0.6.4-2-linux-amd64 --config /etc/velociraptor.config.yaml frontend -v
```

The basic setup of velociraptor is now up and running. We can now start to add clients in our velociraptor environment.
### 4. Adding Windows Client
Edit the `velociraptor.config.yaml` file again.
Scroll down to the first END CERTIFICATE line.
Below the "nonce: line, insert this line, as shown in the image above.
`use_self_signed_ssl: true`
Prepare Client installer for windows:
```
cd Velociraptor
./velociraptor-v0.6.4-2-linux-amd64 --config /etc/velociraptor.config.yaml config client > client.config.yaml
wget https://github.com/Velocidex/velociraptor/releases/download/v0.6.4-2/velociraptor-v0.6.4-2-windows-amd64.exe
./velociraptor-v0.6.4-2-linux-amd64 config repack --exe velociraptor-v0.6.4-2-windows-amd64.exe client.config.yaml repackaged_velociraptor.exe
```

I'm using winscp to transfer the repacked exe file to my windows box

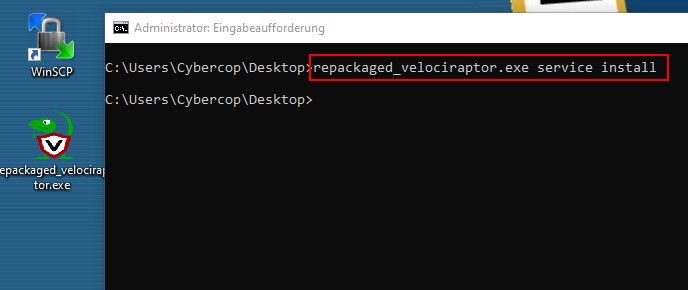
Open a elevated cmd prompt:
```
cd %userprofile%\Desktop
repackaged_velociraptor.exe service install
```
### 5. Viewing the Client

We have now full control over the client, can browse trough the **filesystem** and **registry** or **collecting some artefacts**!


### 6. Collecting first artifact
At the top left, click the house icon to go to the home page, which shows "Server status".
At the top center, click the "**Show All**" button.
In the "Client ID" column, click the blue link.
At the top center, click the **Collected** button.
At the top left, click the plus-sign (see image below)

At the top left, in the search box, type **netstat**.
Click **Windows.Network.NetstatEnriched**.
A description of this artifact appears, as shown below.
At the lower left, click the blue "**Configure Parameters**" link.
At the top left, click the wrench icon.
In the "ProcessNameRegex" field, enter **velociraptor.\*** as shown below.
At the lower right, click the blue **Launch** link.
In the next screen, at the top center, click the **Windows.Network.NetstatEnriched** line to highlight it. In the lower pane, click the **Results** tab.
You see information about the Velociraptor process, as shown below:

As we know the basics, we can practise a little bit ;-)