# Disk acquisition with ewftools

### 1. Introduction
> Image acquisition involves making a copy (or several copies) of the seized hard disk which can be then used to forensics analysis. This allows the investigators to analyze this image while ensuring the integrity and present condition of the real evidence disk.
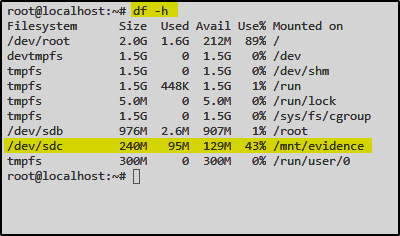
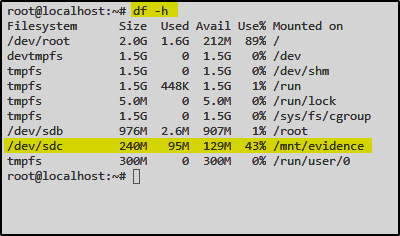
In this lab, the evidence hard disk is mounted on ‘/dev/sdc’. The [**ewf-tools**](https://github.com/libyal/libewf) are installed on the lab machine. The tool uses the Expert Witness Compression Format (EWF).
### 2. Create Image with ewf-tools
First I’ll check if the disk is mounted on the filesystem
`df -h`
To prevent any failures during disk imaging, let’s unmount the disk first
`umount /dev/sdc`
Everything is prepared now to use ewfacquire to create a disk image
`ewfacquire /dev/sdc`
Further you can enter some more informations like Case Number, Description or Examiner name..
For all the other options I’ll leave the default values:
Let’s start the process:
To verify the disk image we can use the following command:
`ewfinfo evidence.E01`
### 3. Summary
{% embed url="" %}